This will be short and sweet and I only post it because it’s hard to find via google but should be base knowledge for any hacker. SysInternals is your friend. If it’s on the box or you can drop it there it gives pretty complete control at a very granular level. Even if you drop one or two of the tools rather than the whole suite it makes privesc a breeze. For example If you have admin, and need System: psexec -i -s “cmd.exe” that is all. Pretty short and easy to read one-liner and good tool for the arsenal.
Tag: privesc
-
Escalating Privilege with ACLPWN.py
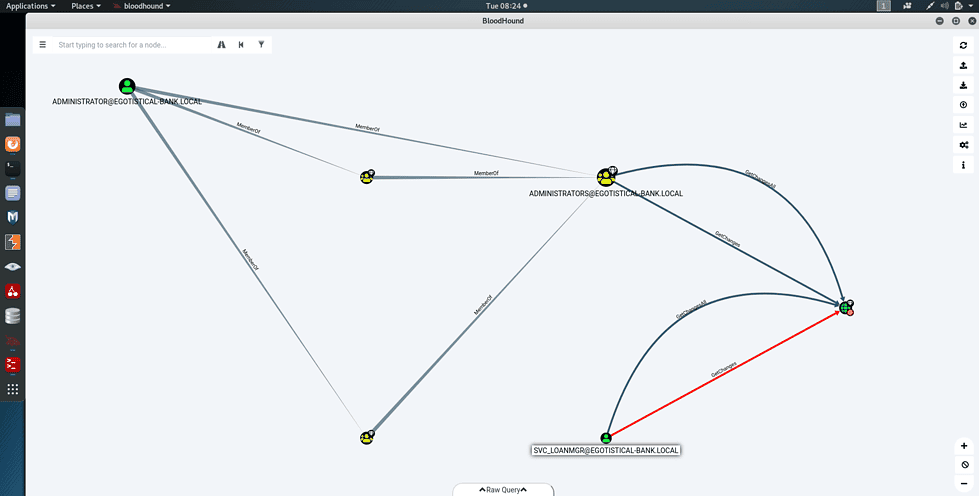
On a recent hacking challenge I was presented with a privesc scenario where I had already compromised a low privileged user with the tools available in Impacket. The user (a service account) had access to winrm and therefore had a semi-functional shell but no access to rdp or smb shares. The network had a default installation of Exchange server, which opens up some avenues for privesc, thanks to the research of dirkjanm and his tool aclpwn.py aclpwn.py uses BloodHound an ActiveDirectory graphing tool to identify paths and exploitation routes on a domain and easily identifies the shortest path from any user to domain admin. aclpwn uses this graph and low level credentials to abuse group memberships created by exchange, specifically the Exchange Windows Permissions group, which for some reason has writedacl privileges in active directory environments. Now my compromised service account wasn’t part of the group and had no write dacl permissions, but could under it’s own authority, create a new user and add it to the necessary group. After bashing the keyboard repeatedly trying to find a way to access the domain with this user, enter aclpwn. Usage is simple. On kali, pip install aclpwn.
aclpwn -f <target> -ft <target-type i.e. user | computer > -d <domain>
You need your BloodHound instance running, and may need to supply it’s credentials
aclpwn -f <target> -ft <target-type i.e. user | computer > -d testsegment.local -du <database user>-dp <database password>
Bang, automatically add your user full privileges to DCSync any or all accounts on the domain. Domain Admin hashes, dumped with impacket , easy-peasy privesc.